New CanisterWorm Targets Kubernetes Clusters, Deploys “Kamikaze” Wiper
HackRead
•
Monday, March 23, 2026
•
Tehran, Tehran Province, Iran
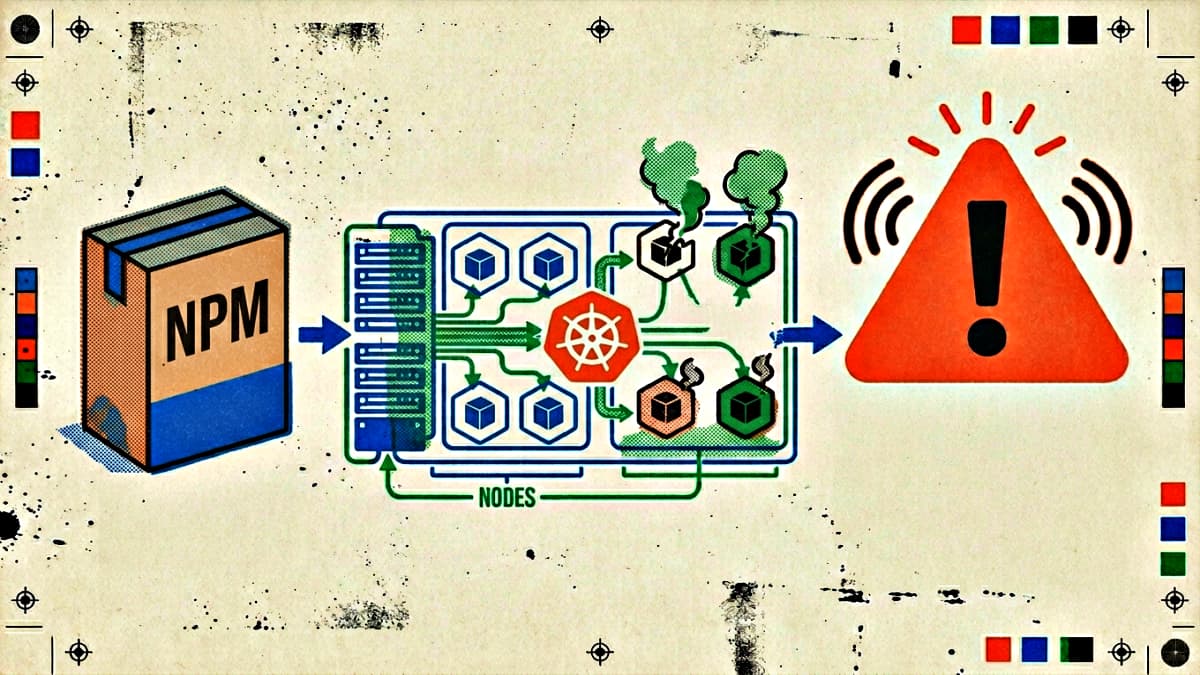
A fast-moving malware campaign dubbed CanisterWorm is spreading rapidly through developer ecosystems, moving between machines in seconds. First observed on 20 March 2026, the campaign escalated within 48 hours from credential theft to destructive attacks against Kubernetes environments. The group behind the activity, TeamPCP, seeded malicious code into more than 45 npm packages. Investigators link the campaign to the earlier compromise of Aqua Security's Trivy scanner. The malware uses a blockchain-based canister on the Internet Computer Protocol for C2. If it detects a Kubernetes network in Iran, it deploys the Kamikaze wiper to delete all files and crash the system. Outside of Iran, it installs a backdoor. It also steals SSH keys for lateral movement and hides under service names like 'pgmon' or 'pgmonitor'.